Wallets are made in such a way that a simple dozen words can reconstruct thousands of addresses. How ?
Wallet BIP-32
We have seen in this article how wallets create a seed. Now let’s see how to create an HD wallet from this seed.
We are talking about Wallet HD for “Hierarchical” and “Deterministic”. In simple terms, this type of wallet ensures that all addresses always derive in the same way from the seed.
Knowing that behind each address is a public key. It’s important to keep that in mind. An address is just a public key encoding. It’s the same thing.
[Notre article sur le sujet : Comment les adresses Bitcoin sont-elles créées ?]
All this is possible thanks to the concept of deterministic key derivation introduced by Peter Wuille in the BIP-32. That is to say that the same seed will always produce exactly the same private/public keys.
In short, BIP-32 greatly simplifies things since a single seed is enough to restore its tens or hundreds of key pairs. Even millions in the case of an exchange.
Note before going further that a wallet can work very well with a single pair of keys. The problem being the ensuing loss of confidentiality. We talked about it HERE. It is therefore better to create a new address (a new pair of keys) for each transaction.
Derive keys from the seed
Here is quickly how to obtain the original seed. It all starts with the generation of an “entropy” which is a random number of 128, 256 or 512 bits.
Let’s take the 128-bit entropy used previously:
0 0 0 0 0 1 1 0 1 1 0 0 1 0 0 1 1 0 0 0 1 0 0 1 0 0 1 1 0 1 0 1 1 1 1 0 1 0 1 1 1 1 0 1 0 1 1 1 0 1 0 0 1 0 1 0 0 0 1 1 0 0 0 0 1 1 0 1 0 1 0 1 0 1 1 0 0 0 1 1 1 1 1 0 0 1 1 1 1 0 0 1 0 1 0 0 1 1 0 0 1 0 0 1 1 0 0 0 1 0 0 1 1 1 0 1 1 0 0 0 1 1 1 0 0 0 0 1
This number is randomly generated and is expressed above in binary (base 2). Which, by the way, corresponds to the number (9,021,802,605,472,555,840,788,517,848,795,437,281) in the decimal system (base 10).
This entropy is used to create the mnemonic phrase (the 12 words) which will be in our case:
Allow Equip essence Stuff Innocent Blue Fever Lamp Net Equip Invite Second
The mnemonic phrase is then converted into a hash via the HMAC-SHA-512 hash function grinder. This resulting hash is the famous 512-bit seed:
b8485829b0151585b9c24ba336811b7274c08d0d44380028f01f7d7e5e5c2e26811cef5b44c9785ffae7341ed8ec6f079a77829136b148b72b73f70ea7d31c02
The seed is expressed here in hexadecimal rather than in bits so as not to take up too much space.
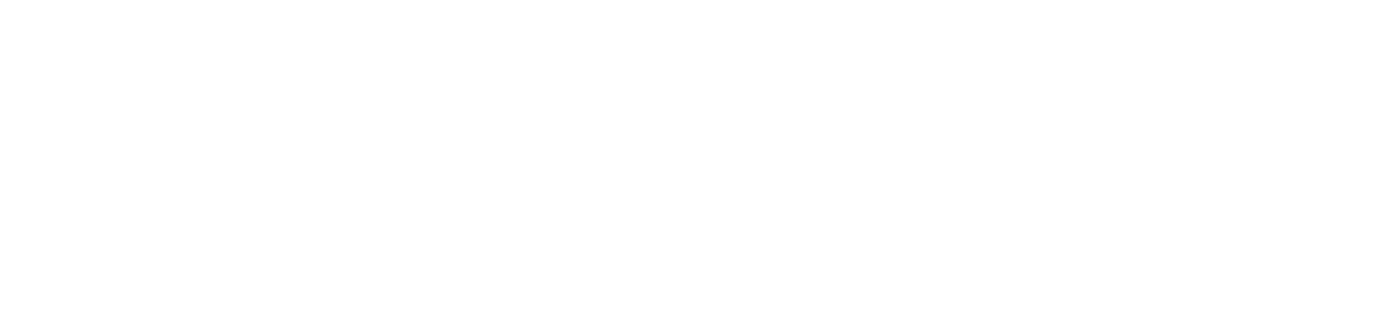
This seed is then split in two to create the Master Private Key (m) as well as the main chain code (c).
The left 256 bits will act as the Master Private Key:
b8485829b0151585b9c24ba336811b7274c08d0d44380028f01f7d7e5e5c2e26
The 256 straight bits will act as the very first string code:
811cef5b44c9785ffae7341ed8ec6f079a77829136b148b72b73f70ea7d31c02
Simple isn’t it? Drawing :
A corresponding master public key (M) is then generated from the master private key (m) using elliptic curve cryptography. This part is less obvious, but we will explain it shortly.
The other key pairs are therefore created according to the same protocol. Except that instead of starting from the seed, we start from the “extended” public key (extended public key, or “Xpub” in the jargon).
This extended public key combines:
-The master public key (or the master private key, as desired)
– An index number. The first derived key will have index #0, the second will have index #1, and so on.
-The channel code.
By putting these three pieces of information together, you therefore obtain an “extended” public key which will again be hashed by HMAC-SHA-512.
This results in a 512-bit hash which is split into two 256-bit halves, one forming the daughter private key and the other a new chain code:
The modification of the index allows to extend the number of child keys 1,2,3, etc. Each extended key can generate more than two billion child keys. And therefore as many bitcoin addresses.
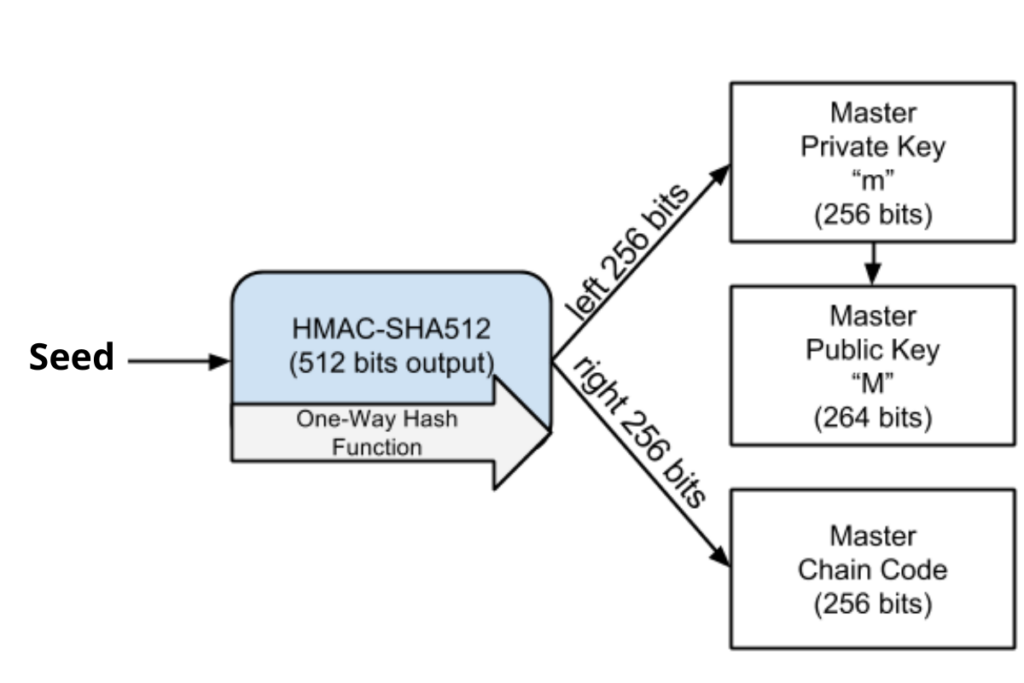
Thus, each child key can become an extended key from which a new series of child keys (a new branch) can be derived:
So. Thanks to the democratization of BIP-32, it is possible to recover all your bitcoins from a mere dozen words.
And since all wallets have adopted this protocol, you can also change wallets like shirts with the same seed.
Receive a digest of news in the world of cryptocurrencies by subscribing to our new service of daily and weekly so you don’t miss any of the essential Tremplin.io!