Global cybersecurity faces a unpublished challenge : Organizations must simultaneously comply with NIS2, prepare post-quantic migration (NIST 2030-2035 deadlines) and implement a truly operational zero-trust. This Convergence of constraints Creates a unique opportunity window for solutions that solve several problems at the same time.

In short
- Naoris Protocol combines post-quantic cybersecurity, zero-trust executable and compatibility EVM.
- His token $ Naoris transforms security into an incentive economy via the Diposec consensus.
- The project meets urgent regulatory needs (NIS2, NIST 2030-2035) with favorable timing.
Noris Protocol is positioned precisely on this intersection with a Decentralized, post-quantic and EVM-compatible safety layer which protects the existing without forced migration while creating an incentive economy via the $ noris token.
For a long -term investor, it is a rare combination: A massive and dated need, a differentiating technical solution, and an architecture designed for institutional adoption.
Why the timing seems favorable
Governments, hospitals, intelligent cities and operators of vital importance face a convergence of critical challenges. There Nis2 directivenow in force since October 2024, imposes new cybersecurity requirements that many organizations are still struggling to fully meet. At the same time, thematurity 2030-2035 set by NIST For post-quantic migration is inexorably closer, creating considerable time pressure.
This emergency is amplified by the concrete threat of the “” Harvest Now, Decrypt Later“” : adversaries massively collect encrypted data today, betting on their ability to decipher them tomorrow with quantum computers. This reality creates an urgent need to secure the infrastructure already exposed.
The main challenge lies in thepractical impossibility of replacing everything at once. Budgetary constraints, technical complexity and operational risks oblige organizations to seek solutions Compatible with the existingcapable of evolving to post-quantic standards unrivaled.
A layer of post-quantic abstraction which secures the existing infrastructure without painful migration responds precisely to these converging temporal and operational constraints.
How Noris resolves the security dilemma vs compatibility
Noris Protocol deploys a revolutionary architecture called “Sub-Zero Layer”which discreetly fits under blockchains and existing systems to secure them without disturbing them. This approach avoids the nightmare of forced migration while providing native post-fantasy protection.
Innovation lies in four interconnected technical pillars:
- Post-quantic protection without disruption : architecture maintains the EVM compatibility existing while integrating Quantum -resistant algorithms Validated by NIST (ML-DSA, ML-KEM), allowing a progressive transition to post-quantic security.
- Transformation of devices into validators : consensus Diposec combined with SWARM AI converts each device to Autonomous safety node who must continually prove its reliability. Compromise devices automatically lose their access rights and their stakes tokens.
- Zero-Trust executable : No more declarative security policies that no one really respects. Here, the network itself applies the rules automatically and measuring.
- Collective resilience : THE Mesh intelligent self-reparesdetects and isolates weak links in real time, guaranteeing continuity of service even under attack.
The economic issue is considerable: if this logic becomes the de facto standard for regulated public and private infrastructure, The token $ noris – who orchestrates, secures and incentives the whole – is positioned at the heart of value creation of a potentially gigantic market.
$ Noris: a utility token, not an accessory
THE $ Noris is used for encourage, secure, measure (remunerate useful detections, sanction risky behavior), and govern the extension of the network.
Based on a model “Device-to-Device Proof of Trust”the token concretely rewards users who participate in the validation of mesh devices. Under the consensus Diposecdevices are valid for each other for trusted behavior with bloc times in milliseconds.
This approach fundamentally transforms the economy of cybersecurity: we go from a cost center traditional at A cybersecurity economy where each actor is paid to improve collective safety. The more the network grows, the more the value of maintaining provable cybersecurity exponentially increases.
Where to trader $ noris?
| Future | SPOT | Dex |
| Binance | Binance Alpha | Uniswap (ETH) |
| Bybit | Bitget | Pancakeswap (BSC) |
| Bitget | Spoiled | |
| Spoiled | Mexc | |
| Mexc | Lbank | |
| Kucoin |
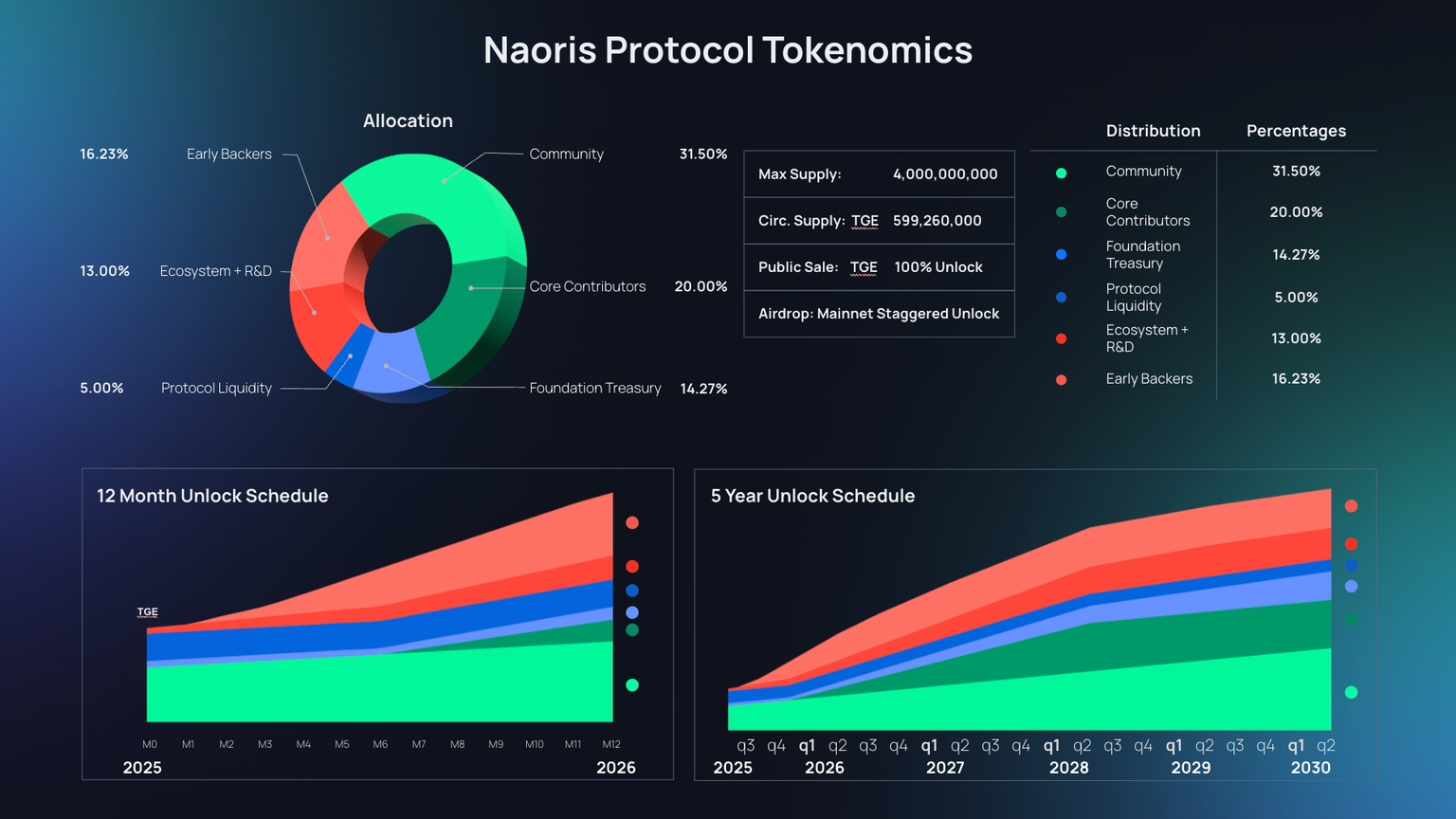
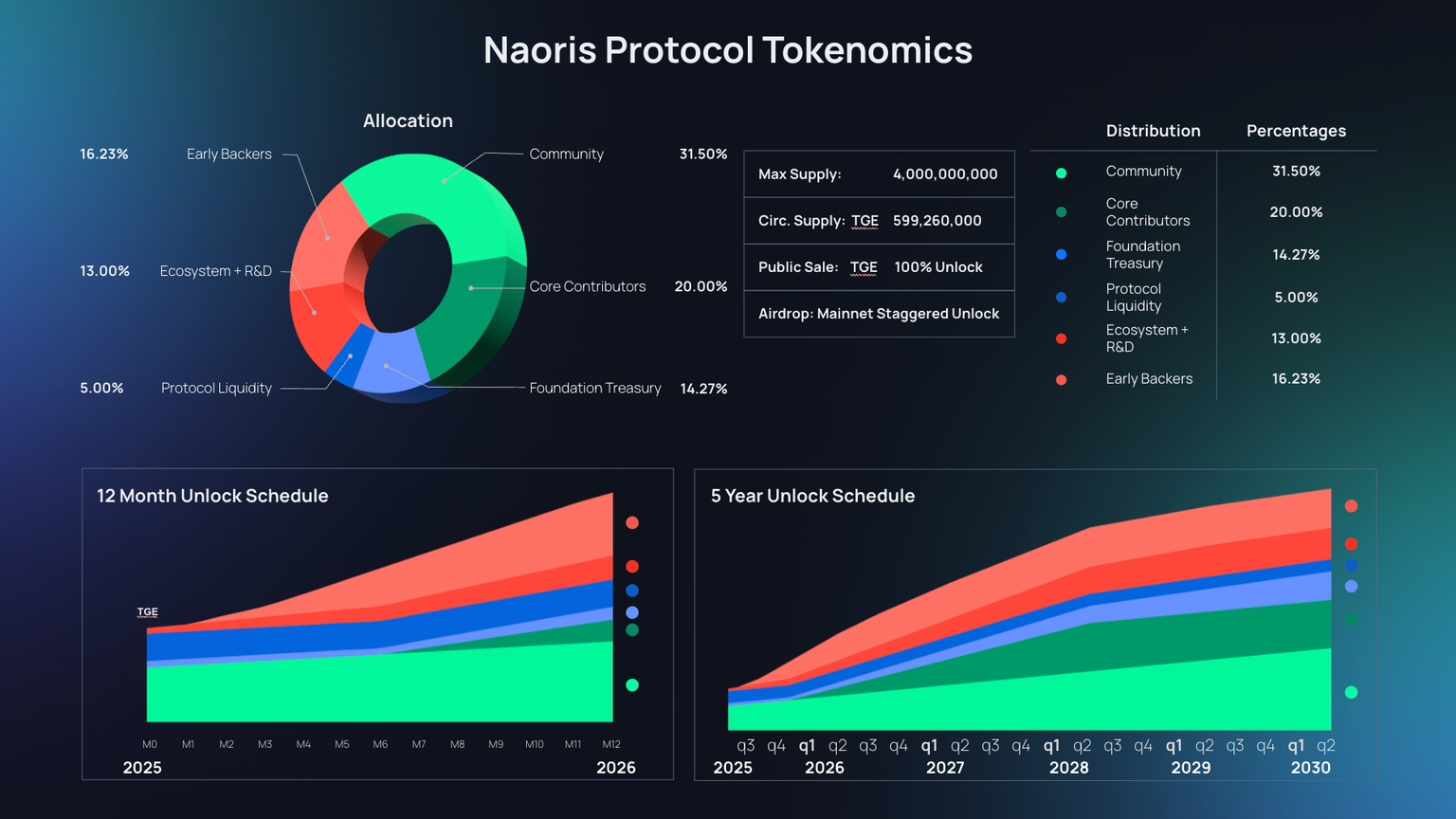
$ Noris tokenomics: a model designed for sustainability
The economic structure favors actual adoption Rather than speculation. With 599.26 million tokens in circulation Out of 4 billion in total, $ Naoris displays a valuation measured for an infrastructure project.
The model directly rewards the Participation in mesh : efficient devices earn tokens, risk behaviors are sanctioned. This mechanics naturally aligns network performance and token value.
The allowance favors Community (31.5%) and Core Contributors (20%)while the early backers represent only 16.23%. The unlocking calendar is spread over 5 years, avoiding massive dumps and promoting long -term commitment.
Key metrics to validate the long -term thesis
- Institutional traction : Public pilots with concrete data (detection time, NIS2/PQC compliance). Without figures, the promise remains theoretical.
- Mesh growth : Evolution of the number of secure devices via DPOSEC. It is the real indicator of organic adoption.
- Post-quantic standards : Effective adoption of ML-DSA/ML-KEM diagrams by industry and demonstrated compatibility.
- Transparent governance : ability to rebalance incentives, rewards/public penalties metrics.
- Interoperability : Web2/Web3 Fluid integrations, absence of disruptive hard forks.
The risks (not to be underestimated)
Despite its potential, Noris Protocol evolves in a complex environment where several factors can compromise the execution of the strategy or significantly delay value creation.
- Slow institutional adoption : Public purchase cycles are notoriously long, weighed down by tender procedures and demanding certifications. Value creation could be shifted far beyond investors' expectations.
- Regulatory uncertainty : The status of the token in the face of emerging executives (Mica, dry) remains vague. Any unfavorable development could impose expensive adjustments on the economic model.
- Technical complexity : The implementation of post-quantity standards and the management of critical updates constitute Points of fragility in an architecture that aims for absolute confidence.
- Giants competition : AWS, Google, Microsoft could reply the architecture Without incentive tokenundergoing the differentiating advantage of the protocol.
The thesis remains ambitious, but evolves on a field where Administrative slowness and absorption power of technological giants will weigh heavy.
Noris Protocol: an infrastructure bet with high potential
Noris Protocol brings together the ingredients of a credible long -term investment thesis : an urgent systemic problem (post-quantic cybersecurity), a binding regulatory framework (NIS2, NIST 2030-2035 deadlines), and a differentiating technical proposition (decentralized mesh + DPOSEC + incentive economy).
- The technical fundamentals are solid : The testnet displays impressive adoption metrics (3.3m+ portfolio, 509m+ neutralized threats), the team combines technical expertise and institutional network, and the sub-zero layer architecture meets the market compatibility needs.
- Timing seems favorable : The TGE of July 2025 opened access to the market at a time when regulatory pressure is intensifying and organizations are looking for concrete post-skills solutions.
- But patience will be put. Institutional adoption cycles are long, real regulatory challenges, and competition from significant technological giants. The creation of value will ultimately depend on the ability to prove real adoption and maintain technological advance.
- For investors : Consider it as a Infrastructure bet on 3-5 yearsdiversify your exhibition, monitor concrete adoption metrics. Governments are progressing slowly, but their equipment decisions are durable.
Disclaimer: The words and opinions expressed in this article engage only their author, and should not be considered as investment advice. Perform your own research before any investment decision.
Maximize your Cointribne experience with our 'Read to Earn' program! For each article you read, earn points and access exclusive rewards. Sign up now and start accumulating advantages.